MyCloudIT deploys RDS for you taking the complexity and time consuming nature out of such...
AVD Build Overview
MyCloudIT deploys AVD for you taking the complexity and time consuming nature out of such operations. Below is an overview of what we built for you
Overview
This article applies to MCIT AVD modern (v3), and does not apply to MCIT classic (v2).
MyCloudIT (MCIT) AVD deployments can “scale up” and “scale out”. Scale up means that you can increase the size of the VMs to support additional users, scale out means that you can add additional VMs as your user load increases.
MCIT automates the Installation, management and monitoring of your AVD deployments within Azure. You take 10 minutes to describe how you want it built and our automation takes the next 1 (approximate) hour to build your AVD solution in Azure. Once it’s built, you have a fully functional AVD deployment.
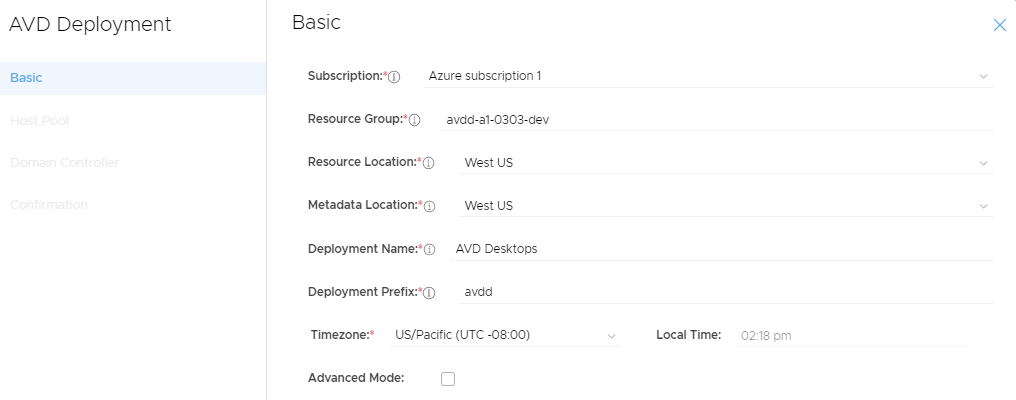
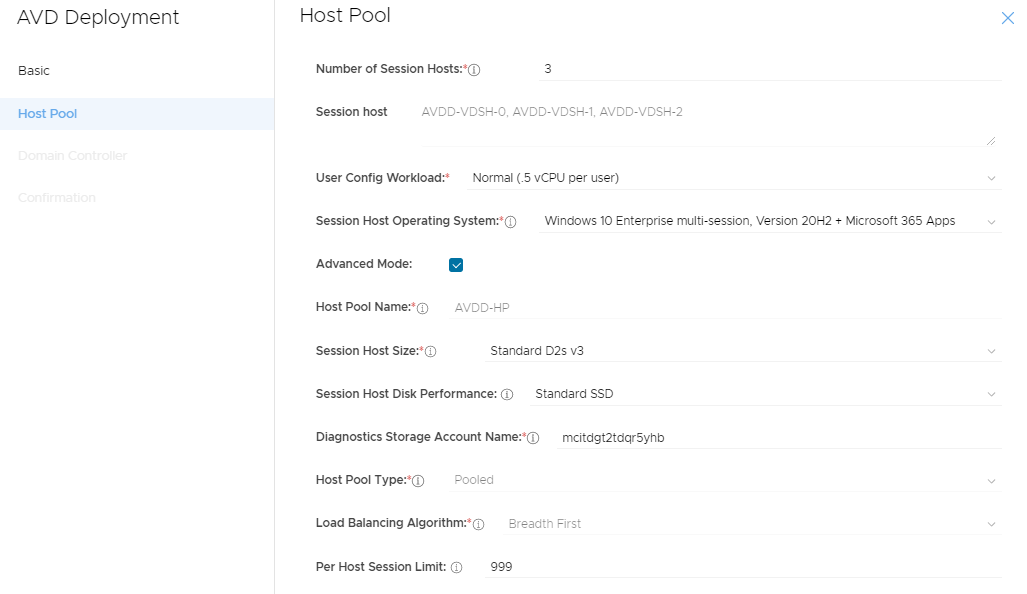
Example Deployment
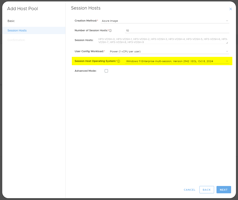
We will show "what we build" for an example small business called "AVD Desktops". Below are the deployment options the customer selected.
MCIT AVD network topology
(click for full image)
Note: The "avdd" resource-name-prefix was selected in deployment.
Default network configurations:
- Name: avdd-Core-SUB
- Address Range: 10.10.10.0/24
- DNS server: 10.10.10.10
- Purpose: Primary infrastructure
- Name: avdd-Workload-SUB
- Address Range: 10.10.20.0/24
- DNS server: 10.10.10.10
- Purpose: Session hosts and other client services
- Name: avdd-DMZ-SUB
- Address Range: 10.10.99.0/24
- DNS server: 10.10.10.10
- Purpose: Public facing infrastructure (empty initially)
Naming Convention: Postfixes used to denote resources
- NET: Azure Virtual Network
- SUB: Azure Virtual Network Subnet
- PIP: Azure Public IP address
- NLB: Azure Network Load Balancer
- LBE: Azure Network Load Balancer Back End
- NSG: Azure Network Security Group
- NIC: Azure Network Interface Card
- SET: Azure Availability Set
- OsDisk: Azure managed disk with the Windows partition
- DataDisk: Azure managed disk for other data such as user profiles
- Note: We do not put a postfix on Azure Virtual Machines as they are limited in name length
VM and Windows Configurations
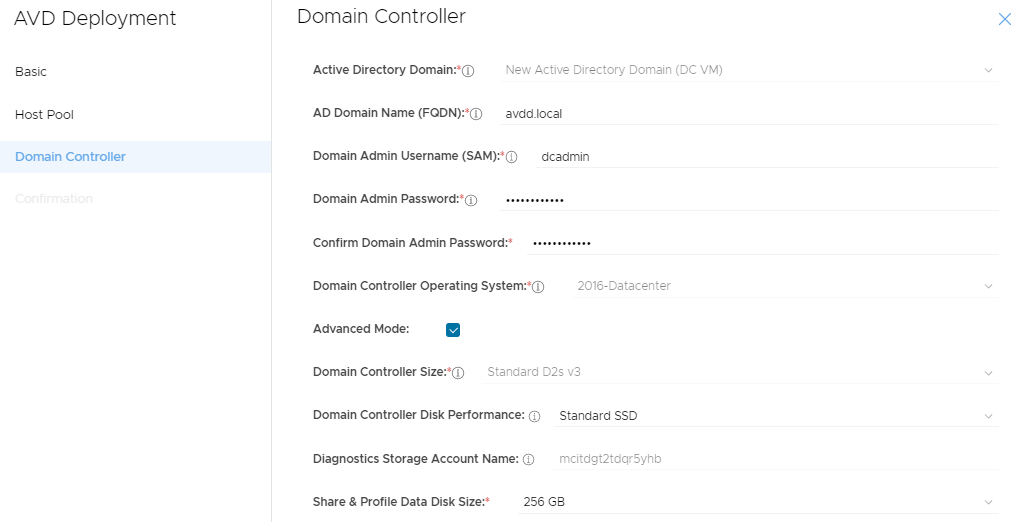
- VM and AD Computer Name: avdd-MSDC-001
- MS Server Roles:
- Active Directory Domain Services (ADDS)
- Microsoft DNS Server (MDNS)
- File Server (FS)
- Other Notes:
- Windows Defender running
- Promoted to ADDS DC holding all FSMO roles
- MCIT custom FSLogix management and installation (user profiles)
- AVD application security group configured
- FSLogix configured for initial SH's and host pool
- Azure AD Connect cloud sync installed and configured
- Default IP address: 10.10.10.10
- Public IP address: Yes, however direct access not allowed by default
- Attached Disks: 1x 128GB OS Disk and 1x Data Disk
- Security Group: Yes via subnet
- Availability Set: avdd-Core-SET
- MS Server Roles:
- VM and AD Computer Name: avdd-VDSH-n (where n is 0 - 999)
- MS Server Roles:
- None
- Other Notes:
- Windows Defender running
- MS Server Roles:
-
-
- Added to the first host pool as a session host
- Depending on option selected may have MS Office 365 installed
- MS AVD agent confirgured
- Can be accessed by end users securely via a web-browser from: https://rdweb.wvd.microsoft.com/arm/webclient
- Default IP address: 10.10.20.n (where n is 4 to 253)
- Public IP address: No
- Attached Disks: 1x 128GB OS Disk
- Security Group: Yes via subnet
- Availability Set: avdd-VDSH-SET
-
Overview Description of Roles
VDSH-n
The Session Host Server(s) provide the end user delivery portion of AVD. Having multiple Session Host Servers is the ideal way to scale your deployment based on user demand. The Session Host Servers are the VMs that deliver resources to the end users. You can customize each Session Host Server after your deployment is created, but it is critical that all Session Host Servers within the same collection be configured identically. This concept is so important, that MCIT allows you to create an initial image of the Session Host Server as a template to be used by all Session Host Servers in a deployment. This is referred to as clone and Golden Image. This Golden Image should be configured for the end user experience you want to deliver to your end users. All the end user applications should be installed on the Golden Image. You can also update this Golden Image as additional applications and patches need to be deployed to your end users.
MSDC-001 (A.K.A Management Server)
The File Server role manages the shares created on the Management Server. Every Management Server has an additional volume attached to it, usually it is the “F:” drive and contains the Active Directory database and the User Profile shares (via FSLogix). FSLogix is used to ensure that whichever Session Host a user is connected to, their personal settings and documents are available (Windows user profile). The Management Server has additional storage capacity to serve as a File Server for user applications and company shares as well.
Each AVD deployment requires access to a Windows Server Active Directory Domain. The AD DS and DNS roles are installed on the management server, and the Management Server is promoted to a Domain Controller of the new Active Directory root forest created within the environment. Additionally Azure AD and the management server AD domain require syncing and this is achieved via Azure AD Connect cloud sync running on the management server.
Normal users never log into the Management Server, but users may access File Shares shared from the Management Server.
Overview of How we integrate into Azure
Services Topology

OAuth 2.0 authentication with Azure AD